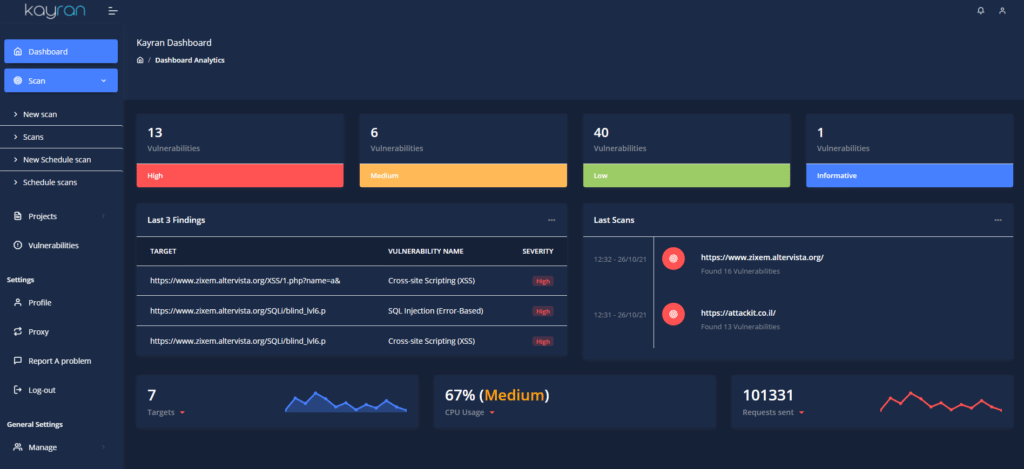
Kayran scanner is helping all businesses, both SMBs and enterprises, to test their online assets and products for over 30,000+ vulnerabilities.
Kayran’s mission is to make penetration testing accessible for all backed by professional cyber security experts holding the same vision and offering their services through Kayran.
Let’s make the world safer, together.
WHAT MAKES KAYRAN SPECIAL ?
Kayran allows you to map weakest points in your web architecture, sort them by severity level and implement patching of the most urgent vulnerabilities first.
With one of the lowest false positive rates in the industry, Kayran pinpoints only legitimate exploitable vulnerabilities using our “Monitoring” System, so you won’t waste time double checking the results.
We currently support over 30,000 vulnerabilities including 10,000 relating to WordPress.
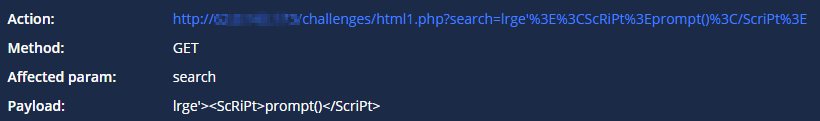
Exploitation
Kayran presents an accurate payload of exploit that was used during our scans, which also includes clear instructions which allow you to replicate the exploitation by yourselves in order to learn about it better.
Single Page Application (SPA)
We are proud to say that our web scanner is the only tool that has the option of scanning SPA websites!
Speed
We use new methods combined with a powerful automation process to reduce server resources and complete the scan at extremely high speeds.
So what’s the story behind Kayran?
Three years ago, we did everything manually, Penetration Testing/investigations, and information extraction.
To multitask, we needed more manpower and a wide range of different tools.
So Sahar Avitan & Eden Zaraf started working on “Kayran”.
Today the tool is able to scan quickly, efficiently, prevent a large number of False positives from other competitors, and exploit vulnerabilities at the highest level.
Kayran is extremely user-friendly, and goes over every piece of information that exists in assets.
In short, join us.







